Miragec/Getty Photos
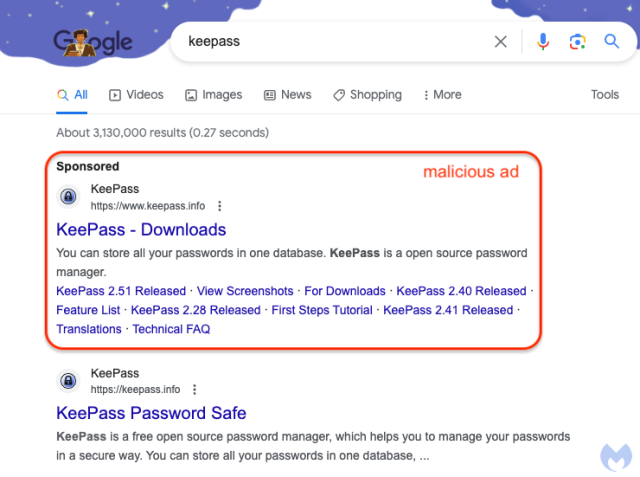
Google has been caught internet hosting a malicious advert so convincing that there’s an honest likelihood it has managed to trick a number of the extra security-savvy customers who encountered it.
Malwarebytes
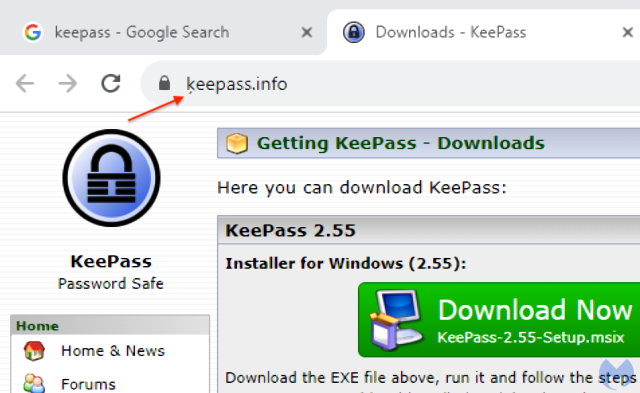
Trying on the advert, which masquerades as a pitch for the open supply password supervisor Keepass, there’s no approach to know that it’s pretend. It’s on Google, in spite of everything, which claims to vet the adverts it carries. Making the ruse all of the extra convincing, clicking on it results in ķeepass[.]data, which, when considered in an handle bar, seems to be the genuine Keepass site.
Malwarebytes
A better take a look at the hyperlink, nonetheless, exhibits that the location is not the real one. Actually, ķeepass[.]data—at the very least when it seems within the handle bar—is simply an encoded method of denoting xn--eepass-vbb[.]data, which, it seems, is pushing a malware household tracked as FakeBat. Combining the advert on Google with an internet site with an nearly an identical URL creates a near-perfect storm of deception.
“Customers are first deceived through the Google advert that appears completely reliable after which once more through a lookalike area,” Jérôme Segura, head of risk intelligence at safety supplier Malwarebytes, wrote in a post on Wednesday that exposed the rip-off.
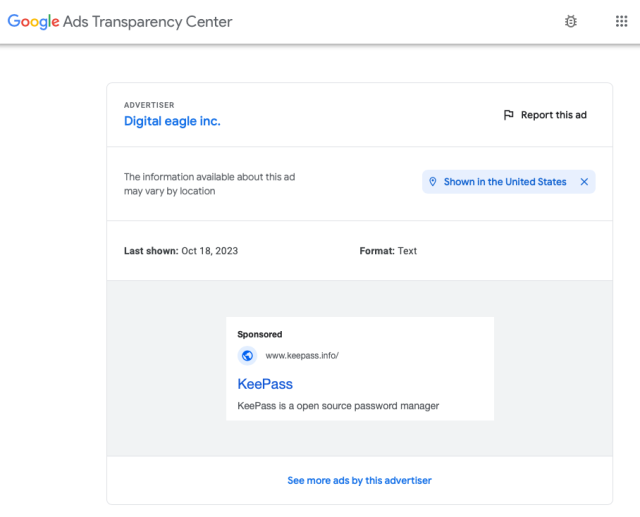
Data from Google’s Advert Transparency Heart exhibits that the adverts have been operating since Saturday and final appeared on Wednesday. The adverts have been paid for by an outfit known as Digital Eagle, which the transparency web page says is an advertiser whose identification has been verified by Google.
Malwarebytes
Google representatives didn’t instantly reply to an e mail, which was despatched after working hours. Previously, the corporate has stated it promptly removes fraudulent adverts as quickly as attainable after they’re reported.
The sleight of hand that allowed the imposter website xn--eepass-vbb[.]data to look as ķeepass[.]data is an encoding scheme generally known as punycode. It permits unicode characters to be represented in commonplace ASCII textual content. Trying fastidiously, it’s straightforward to identify the small comma-like determine instantly under the okay. When it seems in an handle bar, the determine is equally straightforward to overlook, particularly when the URL is backed by a sound TLS certificates, as is the case right here.
Punycode-enhanced malware scams have a protracted historical past. Two years in the past, scammers used Google adverts to drive individuals to a website that appeared almost identical to courageous.com, however was, in truth, one other malicious web site pushing a pretend, malicious model of the browser. The punycode method first got here to widespread consideration in 2017, when a web-application developer created a proof-of-concept website that masqueraded as apple.com.
There’s no surefire approach to detect both malicious Google adverts or punycode-encoded URLs. Posting ķeepass[.]data into all 5 main browsers results in the imposter website. When doubtful, individuals can open a brand new browser tab and manually sort the URL, however that’s not at all times possible once they’re lengthy. An alternative choice is to examine the TLS certificates to make sure it belongs to the location displayed within the handle bar.
