Getty Photos
A now-abandoned USB worm that backdoors related units has continued to self-replicate for years since its creators misplaced management of it and stays energetic on 1000’s, probably thousands and thousands, of machines, researchers mentioned Thursday.
The worm—which first got here to gentle in a 2023 post printed by safety agency Sophos—grew to become energetic in 2019 when a variant of malware generally known as PlugX added performance that allowed it to contaminate USB drives routinely. In flip, these drives would infect any new machine they related to, a functionality that allowed the malware to unfold with out requiring any end-user interplay. Researchers who’ve tracked PlugX since no less than 2008 have mentioned that the malware has origins in China and has been utilized by varied teams tied to the nation’s Ministry of State Safety.
Nonetheless energetic in spite of everything these years
For causes that aren’t clear, the worm creator deserted the one and solely IP handle that was designated as its command-and-control channel. With nobody controlling the contaminated machines anymore, the PlugX worm was successfully lifeless, or no less than one might need presumed so. The worm, it seems, has continued to stay on in an undetermined variety of machines that probably reaches into the thousands and thousands, researchers from safety agency Sekoia reported.
The researchers bought the IP handle and related their very own server infrastructure to “sinkhole” visitors connecting to it, which means intercepting the visitors to stop it from getting used maliciously. Since then, their server continues to obtain PlugX visitors from 90,000 to 100,000 distinctive IP addresses daily. Over the span of six months, the researchers counted requests from almost 2.5 million distinctive IPs. These kinds of requests are commonplace for just about all types of malware and usually occur at common intervals that span from minutes to days. Whereas the variety of affected IPs would not instantly point out the variety of contaminated machines, the amount nonetheless suggests the worm stays energetic on 1000’s, probably thousands and thousands, of units.
“We initially thought that we’ll have just a few thousand victims related to it, as what we are able to have on our common sinkholes,” Sekoia researchers Felix Aimé and Charles M wrote. “Nevertheless, by establishing a easy internet server we noticed a steady circulate of HTTP requests various by way of the time of the day.”
They went on to say that different variants of the worm stay energetic by way of no less than three different command-and-control channels identified in safety circles. There are indications that certainly one of them may have been sinkholed, nevertheless.
Because the picture under reveals, the machines reporting to the sinkhole have broad geographic disbursement:
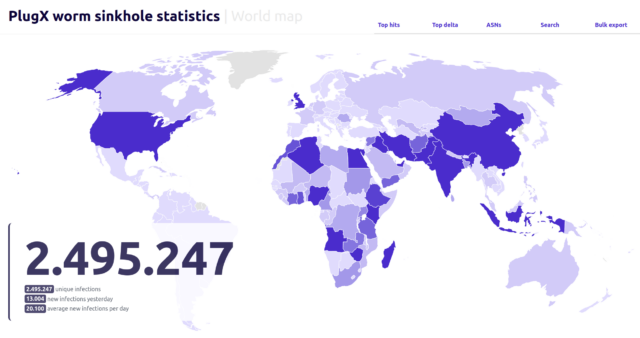
Sekoia
A pattern of incoming visitors over a single day appeared to point out that Nigeria hosted the most important focus of contaminated machines, adopted by India, Indonesia, and the UK.
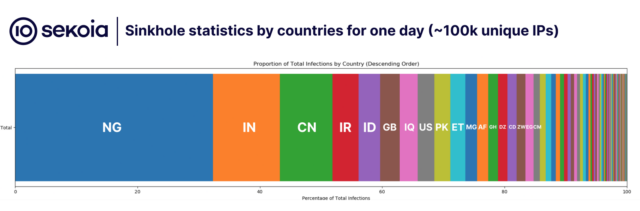
Sekoia
The researchers wrote:
Primarily based on that knowledge, it’s notable that round 15 international locations account for over 80% of the whole infections. It’s additionally intriguing to notice that the main contaminated international locations don’t share many similarities, a sample noticed with earlier USB worms akin to RETADUP which has the very best an infection charges in Spanish spelling international locations. This means the likelihood that this worm might need originated from a number of affected person zeros in numerous international locations.
One clarification is that a lot of the largest concentrations are in international locations which have coastlines the place China’s authorities has vital investments in infrastructure. Moreover lots of the most affected international locations have strategic significance to Chinese language army aims. The researchers speculated that the aim of the marketing campaign was to gather intelligence the Chinese language authorities may use to attain these aims.
The researchers famous that the zombie worm has remained vulnerable to takeover by any risk actor who good points management of the IP handle or manages to insert itself into the pathway between the server at that handle and an contaminated gadget. That risk poses fascinating dilemmas for the governments of affected international locations. They might select to protect the established order by taking no motion, or they might activate a self-delete command constructed into the worm that may disinfect contaminated machines. Moreover, in the event that they select the latter possibility, they might elect to disinfect solely the contaminated machine or add new performance to disinfect any contaminated USB drives that occur to be related.
Due to how the worm infects drives, disinfecting them dangers deleting the professional knowledge saved on them. However, permitting drives to stay contaminated makes it doable for the worm to start out its proliferation another time. Additional complicating the decision-making course of, the researchers famous that even when somebody points instructions that disinfect any contaminated drives that occur to be plugged in, it’s inevitable that the worm will stay on in drives that aren’t related when a distant disinfect command is issued.
“Given the potential authorized challenges that might come up from conducting a widespread disinfection marketing campaign, which includes sending an arbitrary command to workstations we don’t personal, now we have resolved to defer the choice on whether or not to disinfect workstations of their respective international locations to the discretion of nationwide Laptop Emergency Response Groups (CERTs), Regulation Enforcement Businesses (LEAs), and cybersecurity authorities,” the researchers wrote. “As soon as in possession of the disinfection record, we are able to present them an entry to start out the disinfection for a interval of three months. Throughout this time, any PlugX request from an Autonomous System marked for disinfection will likely be responded to with a elimination command or a elimination payload.”
